Introduction: The Perimeter-less Workforce
The office has no walls in 2026. Whether your team is sitting in a central HQ or a home office halfway across the globe, sensitive data is constantly in motion.
Security is an organizational challenge, beyond the remote-only setup. A common mistake is treating Independent Contractors (ICs) with a casual mindset, assuming the risks are different because they are external. In fact, any member of your team represents the same perimeter, regardless of their contract type.
The most effective strategy is mirroring. Your security posture for contractors should reflect the professional standards you already have in place for your internal employees. Remote work is a professional environment, and it requires professional-grade protection. If a protocol is necessary for your staff, it is necessary for your partners.
The goal is to protect your Intellectual Property (IP) and customer data without suffocating productivity. Security needs to be the invisible infrastructure that allows them to work safely.
At Work for Impact, we’ve facilitated over 1.5 million hours of work. That experience has taught us one thing: security failures rarely come from genius hackers. They come from unclear systems, poor documentation, and weak onboarding.
The real enemies of security are ambiguity and complacency. Lapses happen when teams lack standardized procedures, leaving employees to guess the 'safe' way to handle data. They happen when there is a lack of continuous training, causing staff to fall for social engineering attacks that a refresher course could have prevented. They stem from weak password policies and, perhaps most critically, a lack of active monitoring and testing. If you aren't constantly stress-testing your own systems to find the holes, you can be sure someone else eventually will
We built our platform to handle the legal noise and compliance for you, allowing you to focus on the work. This guide is your roadmap to creating your organization's standards and building a secure, high-performance global team.
Key Takeaways: Security for Contractors
- Verified Identity is the Entry Point: Professional trust starts with knowing exactly who is behind the screen. Work for Impact conducts state and federal police checks on all contractors as a non-negotiable minimum.
- The Central Kill Switch: Use Okta or similar SSO tools to grant and revoke access across your entire stack with a single click, eliminating individual logins.
- A Risk-Based Approach: Match your security to your data sensitivity. Use a Zero Trust model for high-stakes assets. Access is granted only after identity and device health are verified against standards like isms.online.
- Share Access, Not Secrets: Stop sending passwords over chat. Use a professional vault like Onepassword to share the ability to work while ensuring your organization retains total ownership of the raw credentials.
- Containment Over Punishment: Treat mistakes as learning moments. Reward fast reporting across the whole team to ensure a "bad click" stays a minor incident.
The Foundation: Verified Identity (The WFI Advantage)
Professional trust starts with knowing exactly who is entering your network. Therefore, verifying identity is a core requirement for any member of a modern workforce. To maintain a unified security posture, your vetting process for contractors should be the same as the professional standards you set for your internal hires.
In 2026, verification needs to be more robust than a quick video call. Generative AI and deepfakes have made identity fraud a technical reality that every organization, on-site or remote, must address. Relying on low-tech methods creates a vulnerability in your foundation.
Bank-Level KYC: Beyond the Scanned ID
We treat identity verification with the same rigor as a global bank. Work for Impact uses financial-grade Know Your Customer (KYC) protocols that look beyond a simple photo ID. Our system utilizes biometric checks, including motion-based liveness detection and anti-spoofing measures.
This technology ensures the person on the other side of the screen is real and matches their verified documentation. In this way, we remove guesswork and replace it with a standardized, professional protocol.
The "Clean Slate" Policy
A verified identity is only the first layer. You need to know the professional history of your partners.
Every contractor on Work for Impact undergoes state and federal police checks as a non-negotiable minimum. This "Clean Slate" policy ensures that everyone entering your inner circle has been vetted for professional integrity and criminal history across global jurisdictions.
The Result: Removing Risk on Day One
- Eliminate Proxy Candidates: You ensure the person doing the work is the person you vetted and hired.
- Compliance at Scale: You don't have to navigate different background check laws in 50+ countries; the system handles the regulatory heavy lifting.
- Immediate Trust: You start the collaboration with a verified partner, allowing you to focus on output rather than identity risks.
By building on a foundation that mirrors corporate-grade vetting, you can focus on the partnership, knowing the entry gate is secure.
The Strategy: Alignment, Documentation, and the "North Star"
If your team views security as a series of bureaucratic hurdles, they will find shortcuts. This is a human tendency across any organization. To prevent it, you must align every partner with the intent behind the rules before handing over the keys. Therefore, security should be your organizational standard, adapted for the role.
Step 1: Define Your "Security North Star"
Move security from an IT checklist to a core company value. Establish a guiding principle that is easy to remember and apply.
- The Rule: "We protect customer data at all costs because their trust is our product."
- The Benefit: When an IC understands that their work directly impacts the company’s primary promise, 2FA and VPNs stop being "friction." They become the professional tools required to do the job correctly.
Step 2: Documentation is Your Operational Manual
To maintain consistency, move beyond verbal instructions. Implement a formal Acceptable Use Policy (AUP) that mirrors your internal handbook but accounts for the specific risks of 2026.
- Standardize for AI: Explicitly define how and when LLMs can be used. Accidental leaks from feeding proprietary code or data into public AI tools are now a leading cause of breaches for all employees.
- Set Device Standards: Define requirements for active antivirus software and the latest OS updates.
- Network Protocol: Set a clear standard against accessing company portals via unsecured public networks without a verified VPN.
Step 3: Formalize the Onboarding Gate
Integrate the AUP into your onboarding flow as a professional requirement.
- The Commitment: Every IC signs the AUP before receiving their first login. This is an operational agreement that they understand and accept your organization's standards.
- Centralized Record: Store the signed commitment where it can be audited, ideally within your project management system or the Work for Impact platform.
Step 4: Maintenance as a System Health Check
A signed document is a baseline. Treat security as an ongoing professional dialogue.
- Quarterly Reviews: Review the AUP with your team every 90 days. As threats evolve, your documentation should cover those changes.
- Collaborative Audits: When everyone is aligned on the "North Star," audits become a simple verification of system health rather than a confrontation.
Security fails when it feels like a hurdle. This checklist ensures your contractors don't just follow rules, but own the process.
1. Define the "Security North Star"
- [ ] The "Why" Test: Have you condensed your security philosophy into one sentence? (e.g., "Customer trust is our only product; we do not compromise it.")
- [ ] Impact Briefing: Have you explained the real-world consequences of a breach to the contractor? (e.g., "A leaked database means we lose X client and your project stops.")
2. Audit Your Documentation (The AUP)
- [ ] AI & LLM Guardrails: Does your policy explicitly state which company data can and cannot be fed into public AI tools?
- [ ] Device Hardening: Are the standards for antivirus and OS updates clearly defined as "entry requirements"?
- [ ] Network Lockdown: Is there a zero-tolerance rule for public Wi-Fi usage without a verified VPN?
3. Formalize the Onboarding Gate
- [ ] No Signature, No Access: Is your system set up to block tool invitations until the Acceptable Use Policy (AUP) is signed?
- [ ] Central Storage: Is the signed commitment stored where both the manager and the contractor can reference it instantly?
4. Maintain the System (Quarterly Cycles)
- [ ] The 90-Day Refresh: Is there a calendar trigger to review the AUP with the contractor every quarter?
- [ ] Threat Update: Have you added new risks (like deepfake fraud or voice cloning) to the handbook in the last 6 months?
When building your security handbook, ensure these five operational points are non-negotiable:
- AI Data Guardrails: Explicitly prohibit feeding proprietary code or sensitive customer data (PII) into public, non-encrypted LLMs.
- Network Protocol: Mandate the use of your Zero Trust tunnel for any connection made outside of a verified, encrypted home network.
- Shadow IT Ban: Define a clear list of approved tools. If a contractor uses an unauthorized app for work, it creates a "data leak" that you can't track or wipe.
- Reporting Incentive: State clearly that accidental clicks won't result in termination if reported within [X] minutes. Speed is the only variable you can control after an error.
The Non-Negotiables: Basic Security Hygiene
These rules are the baseline requirements for any modern employee. To maintain a unified perimeter, your contractors should mirror the same technical hygiene as your internal staff.
By standardizing these three steps, you remove the "easy" entry points and ensure operational consistency across the entire team.
Step 1: Implement Phishing-Resistant MFA
Multi-Factor Authentication (MFA) is the standard defense against credential theft for everyone in the organization. In 2026, we’ve moved beyond SMS codes, which are susceptible to interception, toward more secure, professional methods.
- Standardize the Stack: Every tool, even those perceived as "low-risk," must have MFA enabled. A minor breach in a project management tool can provide the context needed for a major attack elsewhere.
- Professional Authenticator Apps: Mandate the use of tools like Google Authenticator or Authy.
- High-Security Options: For sensitive roles, use hardware keys like YubiKey or biometric Passkeys. These are phishing-resistant and represent the highest tier of account protection.
Step 2: Centralize Access with Enterprise Password Managers
Sharing passwords via chat or spreadsheets is a problem that eventually leads to a crisis. Professional organizations use an Enterprise Password Manager like 1Password or LastPass to govern access.
The strategy here is to share access, not secrets. As the administrator, you create a "vault" and share specific items. The contractor can log in and do their work, but they never actually see or "own" the raw password.
This creates a clean "Kill Switch." When a project ends, you revoke access to the vault instantly. No more manual password resets every time someone leaves the team.
Use this flow to offboard a contractor from a security perspective:
- Identity Deactivation: Shut down the core identity in your SSO (Okta/Google). This instantly severs 90% of their access points.
- Vault Revocation: Remove the user from the shared group in your password manager. Even if they stayed logged into an app, they can't re-authenticate.
- Network Session Kill: Terminate the tunnel session in your Zero Trust console. This blocks access to internal servers and databases immediately.
- Final Audit: Confirm the contract closure on the Work for Impact platform to ensure all deliverables are secure and compliance records are archived.
Step 3: Mandate Verified Network Access (VPN)
You cannot control the network your team uses, whether it's a home router or a co-working space, but you can control how they connect to your assets.
- Reputable Business VPNs: Use tools like NordLayer or Twingate to create an encrypted tunnel for all data.
- IP Allowlisting: These tools allow you to "allowlist" specific static IPs. Your internal servers or databases will then only accept connections coming through the verified VPN tunnel.
By implementing these three non-negotiables, you align your external partners with your internal security posture.
Intermediate & Advanced Security (Risk-Based)
Once the basics are in place, security moves from fixing individual gaps to building an automated system. Professional organizations manage identities. The level of security you apply should reflect the sensitivity of the data involved. Not every role requires a vault, but every role requires a system.
Step 1: Centralized Identity Management (SSO)
For general operations and low-risk data, applying your parent organization’s identity standard is the most efficient move. Instead of a contractor managing 15 different sets of credentials, they use one corporate identity via tools like Okta or Google Workspace Enterprise.
- Standardized Onboarding: You grant access to a predefined group of tools (e.g., "The Design Stack") in one move.
- The Professional Offboard: This is your central "Kill Switch." When a collaboration ends, deactivating one identity instantly locks all doors. You don't have to hunt for every tool they touched.
Step 2: Zero Trust for High-Sensitivity Assets
For roles involving financial records, core codebases, or PII (Personally Identifiable Information), a password is no longer the final proof of identity. We recommend a "Never Trust, Always Verify" model. This is the gold standard for high-security environments.
A Zero Trust system assumes every request is a potential risk until the context is verified. This ensures that even with a correct password, access is only granted if the environment is safe.
- Device Health Verification: The system checks the contractor's device health before granting access. Using standards from isms.online, you can automate a rule: if the OS isn't up to date or the laptop isn't encrypted, the connection is denied.
- Contextual Awareness: If a partner attempts a login from an unusual location or a high-risk IP, the system triggers a biometric re-verification rather than just letting them in.
- Invisible Resources: For high-risk roles, move beyond traditional VPNs. Tools like Twingate or Cloudflare Zero Trust make your internal resources invisible to the public internet.
Using these advanced protocols for your most sensitive data, you remove human error from the equation.
The Human Firewall: Ongoing Training & Simulation
The most sophisticated technical stack can be bypassed by a single human error. Don’t approach security as a "set and forget" task.
Continuous Training
Information decays. Do not expect anyone to remember a long onboarding video from six months ago.
Integrate quarterly micro-trainings into the workflow. Keep them under five minutes. These quick updates should focus on current threats like AI-generated voice scams or new phishing tactics. This keeps security top of mind without requiring hours invested in the process.
Phishing Simulations
You do not know if your training works until it is tested in a real-world scenario.
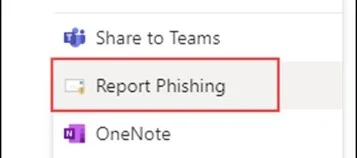
Use tools like KnowBe4 to run regular phishing simulations. Send fake malicious emails to everyone, including your contractors. The goal is to test if they click on suspicious links or provide credentials in a controlled environment.
If they fail the test, do not punish them. Use it as a teachable moment. Immediate, automated retraining is much more effective than a lecture a week later.
Reporting Culture
Treat mistakes as something that can happen. The biggest risk to your data is the time it takes for you to find out about it. In a remote environment, people are often afraid to admit they messed up.
Encourage an environment where reporting a "bad click" is seen as a responsible action. The faster you know a device might be compromised, the faster you can act to protect your assets. Speed of reporting is critical to containment.
Build Your System with Us
At Work for Impact, we help you build the systems that protect your growth. We offer free consultations on security networks and setups to help you align your contractor protocols with your existing organizational standards.
Conclusion
Security is not a one-time project. In 2026, you cannot rely on a single firewall or a "strong" password to protect your company's future.
True security in a perimeter-less workforce is built on three specific layers:
- Verified Identity: Using bank-level KYC and liveness detection to ensure you know exactly who is behind the screen.
- Secure Tools: Enforcing technical barriers like MFA, VPNs, and Password Managers to eliminate the "easy" entry points for attackers.
- Human Vigilance: Turning your partners into an active firewall through micro-training and a transparent reporting culture.
Leverage Our Experience
With over 1 million hours of work facilitated on our platform, we’ve seen every variation of the remote security challenge. Our systems are designed to absorb the "stranger danger" risk before a contractor ever touches your internal tools.
Build on a Solid Base
Scale your security with a verified foundation on Work for Impact. We handle the heavy lifting of bank-grade KYC, biometric liveness checks, and global background screenings so you don't have to.
Build your own internal protocols on top of our verified base. When the foundation is solid, you can focus on the work, not the vulnerabilities.
Ready to Build a Secure Team?
Use the Work for Impact platform to turn these practices into your competitive advantage. Let’s build something that lasts together.